© 2026 Bonfy.AI. All rights reserved.
Shadow AI has moved to the browser—where employees paste, upload, and transform sensitive information in real time, often outside approved tools and governance.
That shift creates a security blind spot because the riskiest behavior happens inside web sessions, before traditional controls can reliably detect or prevent exposure:
The result is real data risk (PII/PHI/PCI exposure, IP leakage, compliance violations) without the visibility or enforcement needed to stop it at the moment it happens.
To manage Shadow AI without blocking productivity, organizations need real-time, content-aware security in the browser—powered by the same intelligence and policies used across email, SaaS apps, collaboration tools, and AI systems.
Bonfy Adaptive Content Security™ (Bonfy ACS™) addresses Shadow AI as a data-centric risk problem, not a “site list” problem:
Because Bonfy is built as a multi-channel platform, this doesn’t add another point tool—it extends one engine for analysis, policy, and enforcement into the browser.
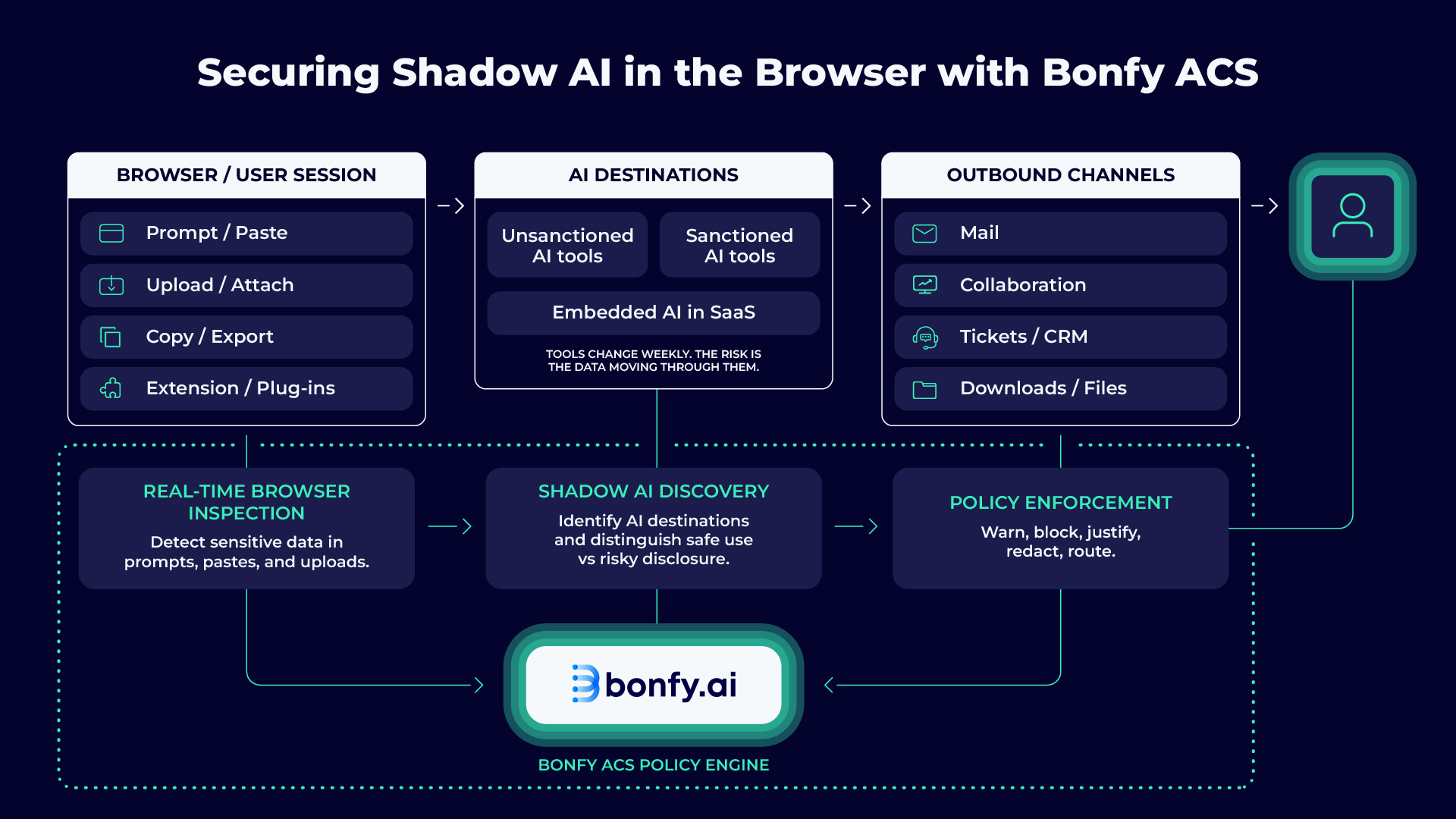
Bonfy secures Shadow AI by applying one consistent brain across the highest-risk browser interactions—prompts, uploads, and outputs—using contextual, entity-aware analysis.
Bonfy’s browser extension performs content-aware inspection of web interactions, including AI prompts and responses, to identify sensitive and regulated data before it leaves the organization.
Bonfy detects unsanctioned AI usage and maps which destinations are in use, what data is flowing, and which users and teams are driving adoption—so you can move from guesswork to governance.
Bonfy can warn users, block specific actions, or require justification when content crosses trust boundaries or regulatory thresholds—grounded in your policies, with clear explanations that reduce workarounds.
Because Bonfy correlates activity across email, SaaS apps, collaboration tools, and AI systems, teams can respond at the entity level—not just the session level—especially when a single user is creating repeated exposures across multiple channels.
Shadow AI increases the speed and reach of data movement, so the same content risks you already manage can escalate quickly when AI is in the loop. Bonfy helps you assess where sensitive data is exposed across modern workflows and prioritize the controls that reduce real-world leakage.

Stop chasing destination lists. Govern the content and the behavior in the browser, even as AI tools change week to week.
Detect and prevent sensitive data exposure in prompts, uploads, and AI interactions before it leaves the organization.
High-accuracy, context-aware guardrails minimize false positives and unnecessary friction—so employees keep moving fast without crossing the line.
Use the same ACS policy brain to govern both unapproved AI usage (Shadow AI) and sanctioned AI that breaks trust boundaries (Shady AI).

© 2026 Bonfy.AI. All rights reserved.