© 2025 Bonfy.AI. All rights reserved.
AI agents are quickly becoming the new interface to enterprise work: summarizing emails, triaging tickets, generating customer responses, and orchestrating actions across internal systems and third-party tools.
But agentic workflows introduce multiple data leakage points that traditional controls weren’t designed to see:
Most “AI agent security” efforts focus on configuration and inventory—what agents exist, what tools they can access, and how they’re set up. That’s necessary, but it doesn’t solve the core problem: the same agent configuration can be used safely or abused, and the real risk lives in the data flowing through the system.
To secure agentic workflows, organizations need a centralized content security plane that can govern:
Bonfy ACS addresses agentic risk with three layers of control, all powered by its entity-aware intelligence, policies, and automation engine.
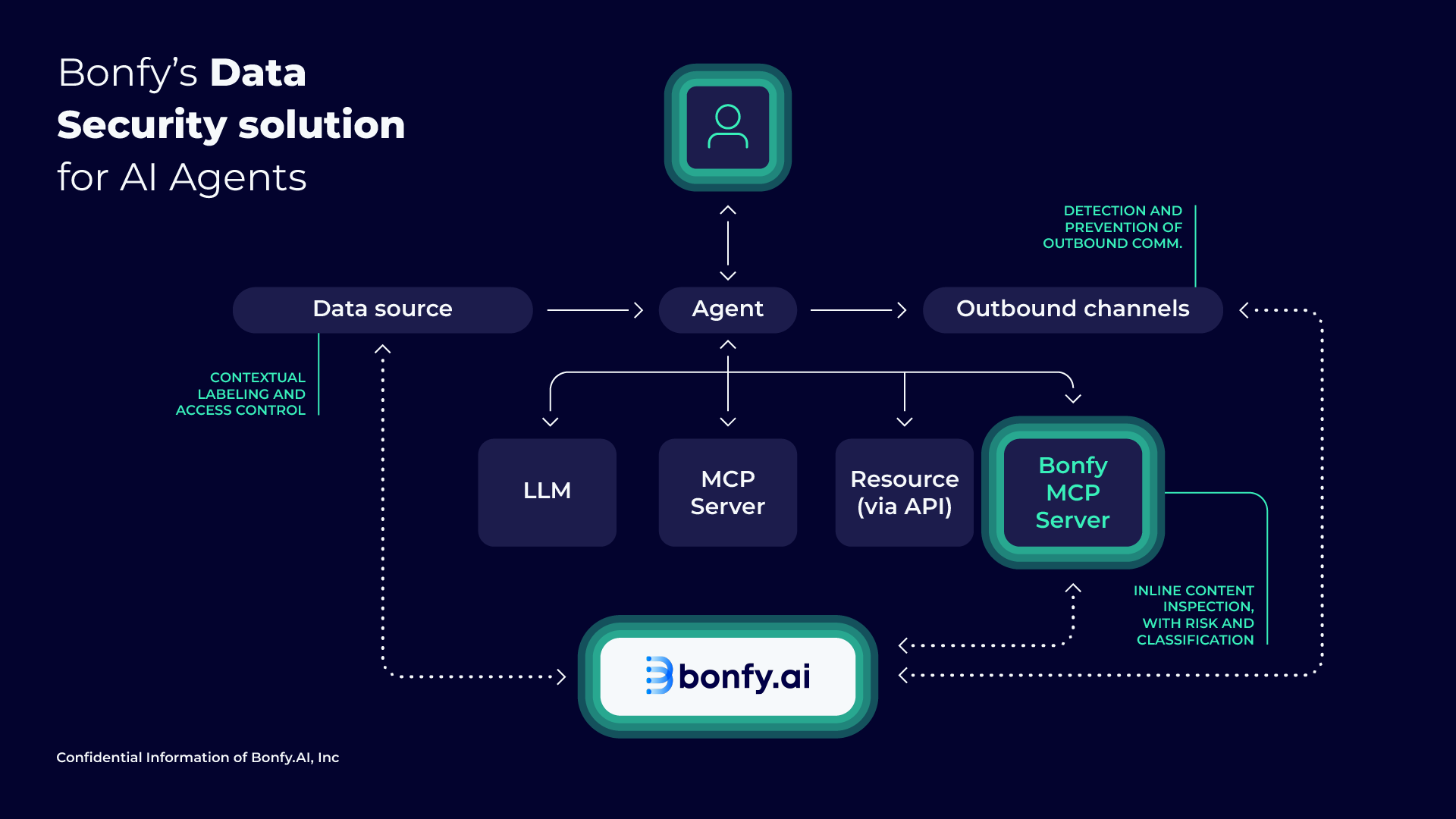
Bonfy secures AI agents by applying one consistent brain across the entire agent data lifecycle—input, output, and data-in-use:
Bonfy helps ensure agents only use the right enterprise data by applying contextual classification and entity-aware governance to what’s available for grounding (ex: controlling what content agents can draw from in systems like file stores and collaboration platforms).
Bonfy inspects what agents produce (emails, documents, tickets, chat messages) before anything is shared externally or broadly internally, preventing:
Bonfy provides its own MCP server that agents can call during their reasoning process to inspect content in real time.
Example: An organization can configure an agent workflow to:
“Summarize these emails—but verify with Bonfy that the summary contains no PII before sending.”
During execution, the agent calls Bonfy’s MCP server to evaluate the content against your policies, and uses the result to decide how to proceed (revise, redact, block, route for review, etc.).
Why it matters: This completes the story of agentic data security. You’re not only controlling endpoints, but you’re also enabling security-aware decision-making inside agent workflows, using the same platform you already trust to govern content across channels.
AI agents increase the speed and reach of data movement, so the same content risks you already manage can escalate quickly when agents are involved. Bonfy helps you assess where sensitive data is exposed across modern workflows and prioritize the controls that reduce real-world leakage.
Automation & response orchestration
Route, block, label, quarantine, notify, or log to security tooling, based on policy and risk level.

Secure the full agent lifecycle: inputs, outputs, and data-in-use inspection via MCP.
Enable adoption at scale with guardrails that work in real workflows, not just policy docs.
Contextual, entity-aware detection reduces noise and supports prevention-ready enforcement.
Avoid point-tool sprawl by using one engine and policy plane across unstructured data and AI workflows.

© 2025 Bonfy.AI. All rights reserved.