© 2025 Bonfy.AI. All rights reserved.
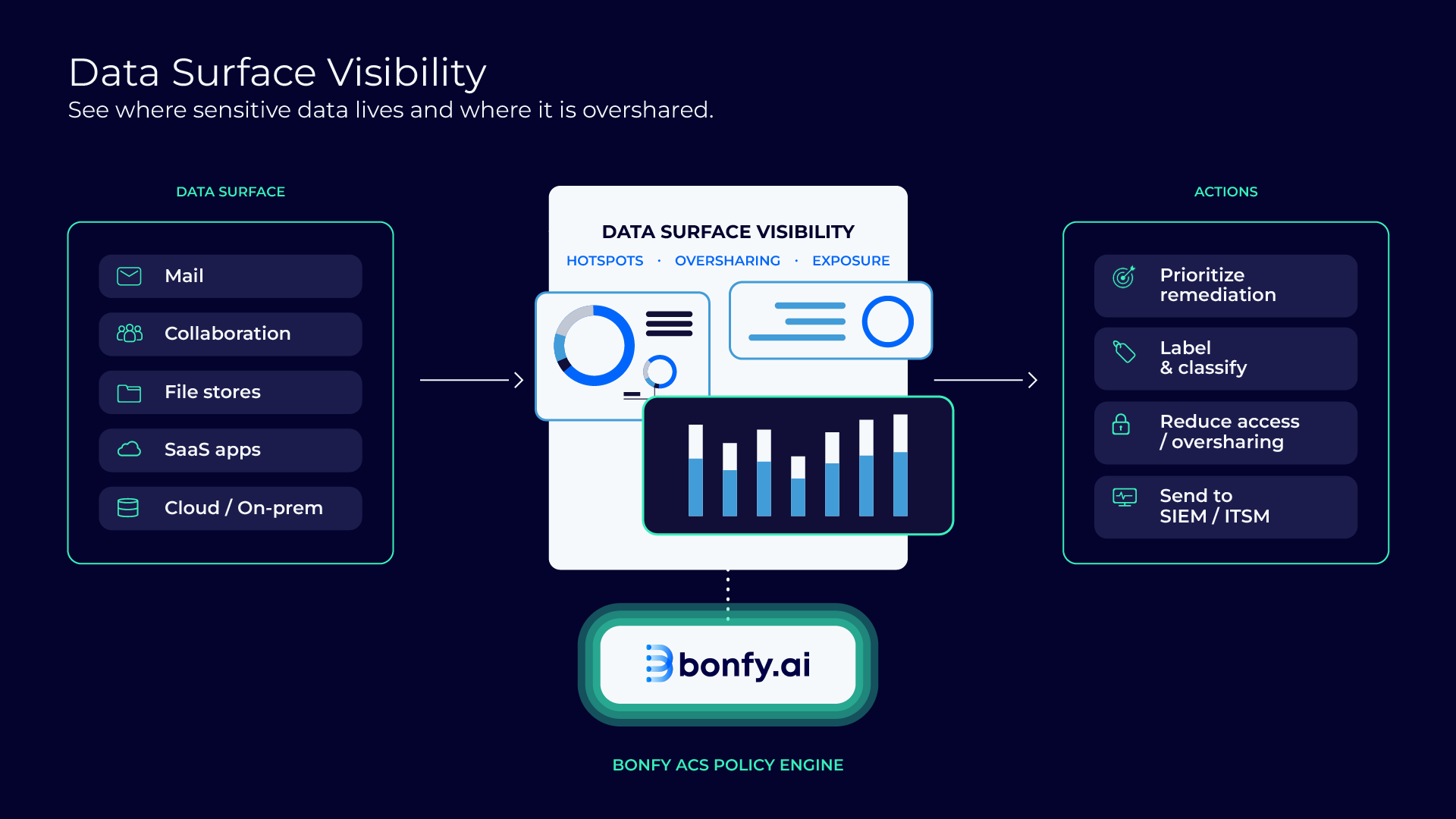
As AI adoption accelerates, most organizations still cannot answer a basic question: Where does our sensitive unstructured data live, and how is it moving?
Most security dashboards focus on isolated activities or incidents. That leaves the unstructured data surface fragmented across collaboration platforms, file stores, and AI-era systems. Without a clear map, teams struggle to:
This creates a familiar pattern. Teams make high-stakes decisions about AI enablement and data security without a reliable view of what they are protecting.
Bonfy Adaptive Content Security™ (Bonfy ACS™) includes a Data Surface Visibility experience that gives CISOs and security teams a live map of:
Instead of only surfacing incidents, Bonfy helps teams understand the shape of their data surface. This makes it easier to identify hotspots, quantify exposure, and focus remediation on what reduces real business risk.
This matters even more in the AI era. Content that is overshared, misclassified, or concentrated in the wrong place can become AI-accessible quickly and increase downstream disclosure risk.
Bonfy’s Data Surface Visibility helps teams understand unstructured data risk quickly, then act on it with confidence as they drill in.
Bonfy provides a high-level view of where sensitive content resides across key repositories and systems. This makes exposure patterns visible, including trends that do not show up in incident-only dashboards.
Bonfy helps teams spot where customer data, PII, IP, or regulated content is concentrated, widely accessible, or overshared. That allows remediation to start with the areas that matter most.
From the high-level view, teams can drill into specific areas to understand:
This makes it easier to focus controls on the business risk behind the exposure.
Visibility is most valuable when it leads directly to a plan. Teams use this view to prioritize:
AI increases the speed and reach of data movement. Unstructured data that is overshared or poorly governed becomes a faster path to exposure. Bonfy helps you assess where sensitive data is exposed across modern workflows and prioritize the controls that reduce real-world leakage.
Automation & response orchestration
Route remediation tasks, label content, notify owners, restrict sharing, or integrate with security tooling based on policy outcomes and risk level.

Get a live view of where sensitive data resides across repositories and systems, beyond a stream of alerts.
Spot hotspots for customer data, PII, IP, and regulated content, then focus cleanup and governance where it reduces risk most.
Understand how sensitive content is accessed and used by people and AI-era workflows.
Use visibility to guide labeling, access decisions, and guardrails so AI adoption stays aligned with your ability to control sensitive content.

© 2025 Bonfy.AI. All rights reserved.